API Checklist for Visa Status Webhooks and Notifications

Visa applications are asynchronous by nature. A traveler submits documents, a government portal reviews them, a payment settles, an eVisa is issued, or a correction is requested. If your product relies on customers manually checking a status page, you create unnecessary support load and real risk close to departure.
Webhooks and notifications fix this, but only when they are implemented with the same discipline you apply to payments: strong security, clear event semantics, idempotency, retries, and observability.
Below is a practical API checklist for visa status webhooks and notifications that product and engineering teams at OTAs, airlines, cruise lines, TMCs, and travel platforms can use to ship a reliable visa-status experience.
What “visa status” really means in an API integration
In online visa processing, “status” is rarely a single field. It is a lifecycle that spans:
- Customer identity capture and document collection
- Application submission to a provider or authority
- In-review steps (automated checks, manual review)
- Follow-ups (additional documents, corrections, interviews, biometrics)
- Final decision (approved, refused, expired, canceled)
That means a webhook integration is not just plumbing. It becomes part of your operational compliance layer: it determines who gets contacted, what your support team sees, and whether a traveler is alerted early enough to take action.
A good model is event-driven updates (webhooks) with a fallback read path (a status endpoint) for reconciliation.
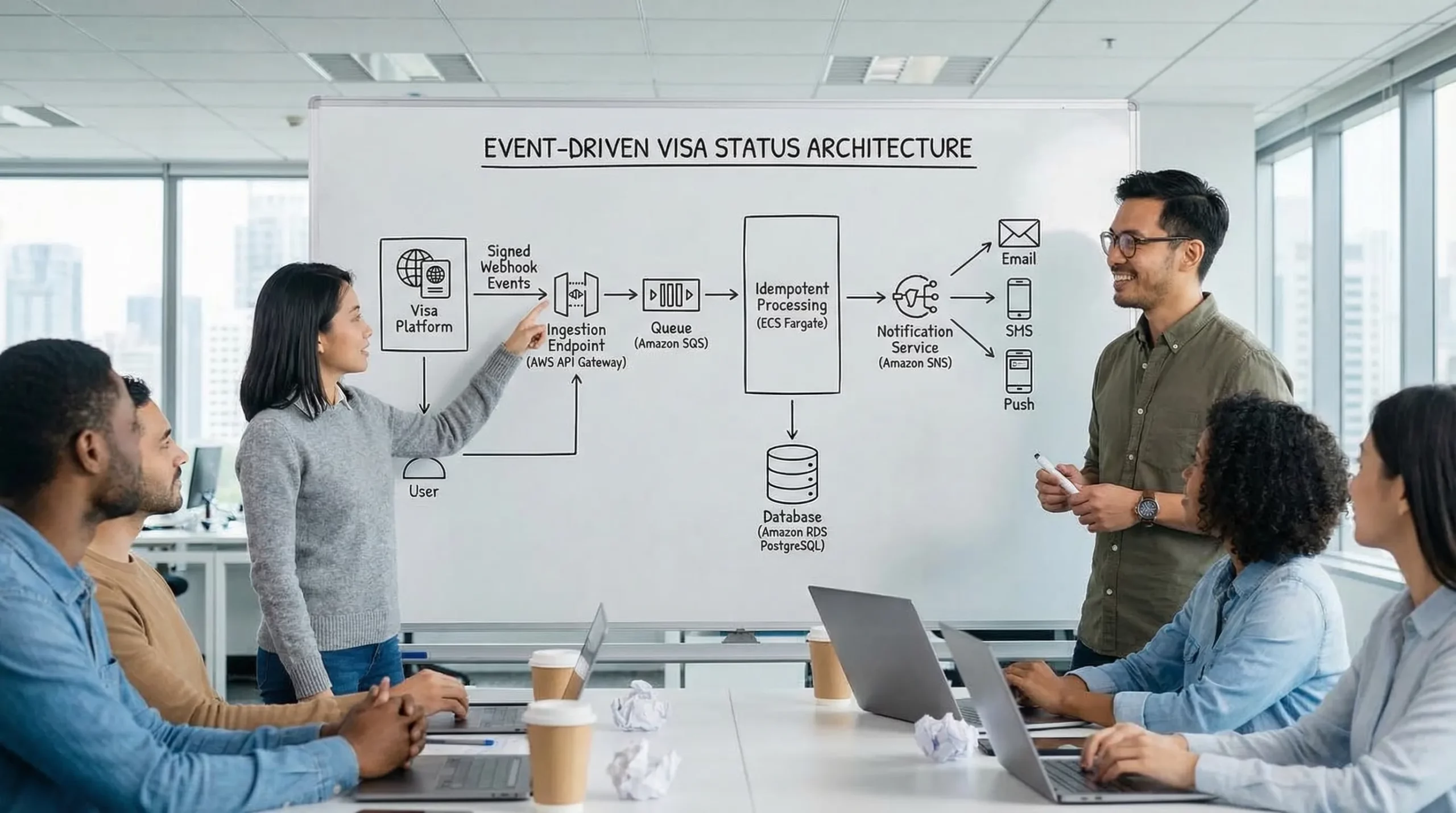
Reference architecture: webhooks plus a reconciliation read
A robust approach is:
- Visa provider sends a webhook event when the application changes state.
- Your system acknowledges quickly, validates authenticity, and enqueues for processing.
- A worker processes the event idempotently and updates your booking, CRM, and traveler record.
- Your notification service decides whether to alert the traveler and via which channel.
- A scheduled reconciliation job periodically calls the status endpoint for “at risk” cases (for example, travel within 72 hours).
Checklist 1: Define the webhook contract (event types, payload, versioning)
Before you implement anything, lock down the contract. This is where most downstream confusion starts.
1) Event taxonomy: state changes, not “everything changed”
Define webhook event types as meaningful state transitions, not generic “updated” events.
Examples of typical visa lifecycle events:
application.createdapplication.submittedapplication.in_reviewapplication.action_requiredapplication.approvedapplication.refusedapplication.canceleddocument.receiveddocument.rejected
Keep the set small and composable. You can always add event types later, but removing or redefining them is costly.
2) Payload minimum viable fields
Treat webhook payloads as “signals” and keep them stable. A common pattern:
{
"id": "evt_01J9...",
"type": "application.action_required",
"created_at": "2026-03-15T21:10:50Z",
"data": {
"application_id": "app_123",
"booking_reference": "ABC123",
"status": "action_required",
"reason_code": "passport_scan_blurry",
"deadline_at": "2026-03-18T23:59:59Z",
"travel": {
"departure_at": "2026-03-22T10:15:00Z",
"destination_country": "GB"
}
},
"schema_version": "2026-01"
}
Recommended fields to include:
id(event ID, globally unique)type(event type)created_at(provider-side timestamp)- A stable entity identifier (
application_id) - A correlation identifier you can map (
booking_referenceor your ownexternal_id) schema_version
3) Schema versioning policy
Adopt explicit versioning early:
- Additive changes should not break existing consumers.
- Breaking changes must come with a new
schema_versionand a migration window. - Avoid renaming fields, deprecate instead.
A simple way to operationalize this is a contract test suite (even a JSON schema check in CI) that validates example payloads from your provider.
4) Put the contract in a table your whole org can read
This avoids tribal knowledge and reduces support escalation churn.
| Contract element | Decision to make | “Good default” |
|---|---|---|
| Event types | What triggers a webhook | Only meaningful state transitions |
| Correlation key | How you map to booking/traveler | external_id set at create time |
| Schema version | How breaking changes are handled | Version string in every event |
| Required fields | What must always be present | id, type, created_at, application_id, schema_version |
Checklist 2: Delivery semantics (ack, retries, idempotency, ordering)
Webhooks are “push”, but they are still a distributed system. Assume events can be duplicated, delayed, or delivered out of order.
1) Acknowledge fast, process async
Your webhook endpoint should:
- Validate signature and basic shape
- Return
2xxquickly (ideally within a couple seconds) - Enqueue for internal processing
Avoid doing heavy work in the request thread (PDF parsing, database joins, sending emails). That is how you trigger provider retries and event floods.
2) Idempotency is non-negotiable
To handle duplicates safely:
- Store
event_idin a durable “processed events” table - Enforce a unique constraint on
event_id - If you receive the same event twice, return
2xxand do nothing
Idempotency should be applied at the event level and, where possible, at the entity update level (for example, only move status forward if the event is newer).
3) Don’t assume ordering
If two events arrive in the wrong sequence (for example, approved then in_review), your state machine should:
- Use event timestamp plus a monotonic provider sequence number if available
- Reject invalid backward transitions
- Prefer a reconciliation read when conflicts occur
4) Define retry behavior explicitly
Work with your provider to understand:
- Retry schedule (exponential backoff vs fixed)
- Maximum retry duration
- Whether retries are per event or per endpoint
If you control the webhook sender (for example, inside your own visa management platform), document this behavior for partners.
Checklist 3: Security controls (webhooks are an attack surface)
Visa status payloads often contain PII and travel intent. Treat webhook ingestion like a sensitive auth surface.
1) Use signature verification and replay protection
Common patterns:
- HMAC signature header (for example,
X-Signature) - Timestamp header (for example,
X-Timestamp) - Verify:
HMAC(secret, timestamp + "." + raw_body) - Reject if timestamp is older than your tolerance window (for example, 5 minutes)
If you are integrating with SimpleVisa, see their developer guidance on authentication and webhook signature verification for implementation details: best practices for authenticating against the SimpleVisa API.
2) Require TLS and harden the endpoint
Baseline controls:
- TLS only, modern ciphers
- Strict request size limits (to prevent payload abuse)
- Rate limiting (even if the provider “should not” exceed it)
- Optional IP allowlisting (useful, but do not rely on it alone)
3) Secrets rotation and environment isolation
Operationally:
- Separate secrets for sandbox and production
- Provide a rotation mechanism that supports overlap (old and new valid for a period)
- Store secrets in a vault, not in app config files
4) Data minimization
Only store what you need:
- If the webhook includes large documents or images, store references, not raw blobs, unless required.
- Apply retention policies aligned to your legal and operational needs.
Checklist 4: Observability and runbooks (your future self will thank you)
Visa status issues tend to show up at the worst time, the day before travel. Observability is what prevents “all hands” incidents.
What to log on every event
Log structured fields so you can search quickly:
event_id,event_type,application_id,external_idsignature_valid(true/false)- Processing outcome (
processed,ignored_duplicate,reconciled,failed_validation) - Latency timestamps (received, queued, processed)
Metrics and SLOs to set
| Metric | Why it matters | Example target |
|---|---|---|
| Webhook ingestion success rate | Detect auth or provider issues | 99.9% 2xx |
| Queue lag (p95) | Prevent late traveler notifications | < 60 seconds |
| Processing failure rate | Detect schema drift and bugs | < 0.1% |
| Time to traveler notification (p95) | Direct customer impact | < 2 minutes |
Alerting triggers that are worth paging for
Alert on symptoms that affect travelers:
- Sudden drop in webhook volume (possible delivery outage)
- Spike in signature verification failures (possible secret mismatch or attack)
- Queue lag exceeding threshold (notifications delayed)
- Reconciliation job detecting mismatches above baseline
Make sure you have a runbook that answers: “What do we tell support and affected travelers while engineering is investigating?”
Checklist 5: Notification rules (when to message travelers, and when not to)
A webhook event is not automatically a customer notification. You need a notification policy that balances urgency with noise.
Use “traveler impact” as the trigger
Good notification triggers:
- Action required (documents missing, payment failed)
- Approval issued (deliver the eVisa or confirmation)
- Refusal issued (clear next steps and escalation paths)
- Approaching departure with pending status (proactive warning)
Avoid notifying on every internal transition that does not change traveler action.
Map statuses to messages and urgency
| Status / event | Traveler impact | Recommended channel | Message intent |
|---|---|---|---|
action_required |
High, blocking | Email + in-app, SMS if close to departure | “You must upload X by deadline” |
approved |
Positive, time-sensitive | Email + in-app | “Your eVisa is approved, download/save it” |
refused |
High, needs clarity | Email + in-app | “Decision received, options and support path” |
in_review (long-running) |
Medium | In-app only, optional email based on SLA | “Still processing, expected next update” |
submitted |
Low | In-app only | “We received your submission” |
Time-to-departure escalation
Tie messaging to the itinerary. An in_review status 30 days out is normal, the same status 24 hours out is an incident.
A practical approach is to compute “risk tiers”:
- Green: departure is far, no action required
- Amber: within a configurable window (for example, 7 days) and still not approved
- Red: within 72 hours and still not approved or action required
Risk tiers drive both traveler messaging and internal support escalation.
Template hygiene (compliance and conversion)
Notification templates should:
- Repeat key identifiers (booking reference, traveler name, destination)
- Avoid exposing unnecessary PII in SMS
- Include clear calls to action (upload link, status page)
- Be localized if you sell globally
Checklist 6: Testing, sandboxing, and rollout
Ship webhooks like you ship payments: test end-to-end, then roll out gradually.
Key practices:
- Use a sandbox environment with realistic event sequences and retries.
- Support event replay in lower environments (either from the provider or your own stored payloads).
- Add contract tests for every event type you rely on.
- Run a canary release (send webhooks to a new endpoint for a subset of traffic, then ramp).
- Verify that notifications fire correctly, especially “action required” and “approved”.
Checklist 7: Integrate visa status into the rest of your stack
Visa status changes often need to touch more than the traveler UI:
- Booking operations: mark “travel-ready” vs “at risk”
- Customer support: sync status into the case/ticket view
- Finance: reconcile refunds, chargebacks, revenue share, ancillary revenue attribution
- Analytics: measure attach rate, completion rate, time-to-approval
If you are a mid-market travel business and need help connecting visa webhooks into ERP and integration-heavy environments, a specialist managed-service partner can accelerate delivery. Teams like DataOngoing’s AI and system integration consultants are built for exactly this kind of cross-system automation work.
Where SimpleVisa typically fits in this flow
SimpleVisa is designed to help travel businesses simplify border-crossing administration with visa processing automation, options for API integration in booking flows, and alternatives such as a white-label visa application app or custom data services.
If you are building visa status webhooks and traveler notifications now, the fastest path is usually:
- Start with a clear event contract and signature verification
- Build a queue-backed ingestion pipeline with strict idempotency
- Add notification rules tied to departure date and action required states
- Layer reconciliation reads for high-risk departures
To explore implementation options (API, white-label, or no-code), you can review SimpleVisa’s integration materials at simplevisa.com and align the webhook design with your desired customer journey and ancillary revenue goals.