Real-Time Rule Changes: How to Sync Visa Data in Your App

Visa and entry requirements change more often than most travel apps are designed to handle. A new electronic travel authorization (eTA), a fee update, a passport-validity tweak, or a transit rule clarification can turn a “confirmed” itinerary into a denied boarding, a last-minute support scramble, or a chargeback.
If your app sells travel or manages trips, syncing visa data is not just a compliance detail. It is a product reliability problem.
This guide breaks down the engineering patterns that work in practice for real-time rule changes, including data modeling, update delivery, caching, versioning, audit trails, and observability. The goal is simple: keep eligibility guidance accurate at every step of the customer journey, without degrading performance or developer velocity.
What “visa data” actually includes (and why it changes)
Most teams underestimate the scope of “visa rules” until the first incident. In production, visa data usually spans:
- Eligibility: nationality, residence, passport type, prior travel history edge cases.
- Document type: visa-free, eVisa, eTA/ETA/ESTA, consular visa.
- Passport constraints: validity window, blank pages (for some regimes), damaged passport policies.
- Itinerary constraints: one-way vs round-trip, maximum stay, 90/180 rules, onward ticket requirements, transit exceptions.
- Purpose of travel: tourism vs business vs work, activities allowed, invitation-letter requirements.
- Operational details: typical processing times, cutoff timing recommendations, required uploads.
- Fees and payment rules: government fees, service fees, currency, refundability.
Rules change because governments adjust policy, launch new digital authorizations, expand pilots, or react to operational pressure (peak seasons, security posture changes). In 2025 and 2026, Europe’s ETIAS program and the UK’s ETA rollout are two prominent examples of systems that force travel sellers to treat rule changes as “always on” rather than “annual updates.”
For official program references, see the EU’s ETIAS information pages and the UK ETA guidance on GOV.UK.
The core product risk: stale rules at the wrong moment
Stale visa rules create three recurring failure modes:
- False reassurance: your app says “No visa required,” but a new authorization is now mandatory.
- False friction: your app blocks a traveler who is actually eligible visa-free (conversion loss).
- Mismatch across surfaces: website, mobile app, email, support scripts, and check-in tools disagree.
From an engineering standpoint, syncing visa data is about guaranteeing consistency and freshness at key decision points while still keeping latency and uptime acceptable.
A practical architecture for syncing visa data
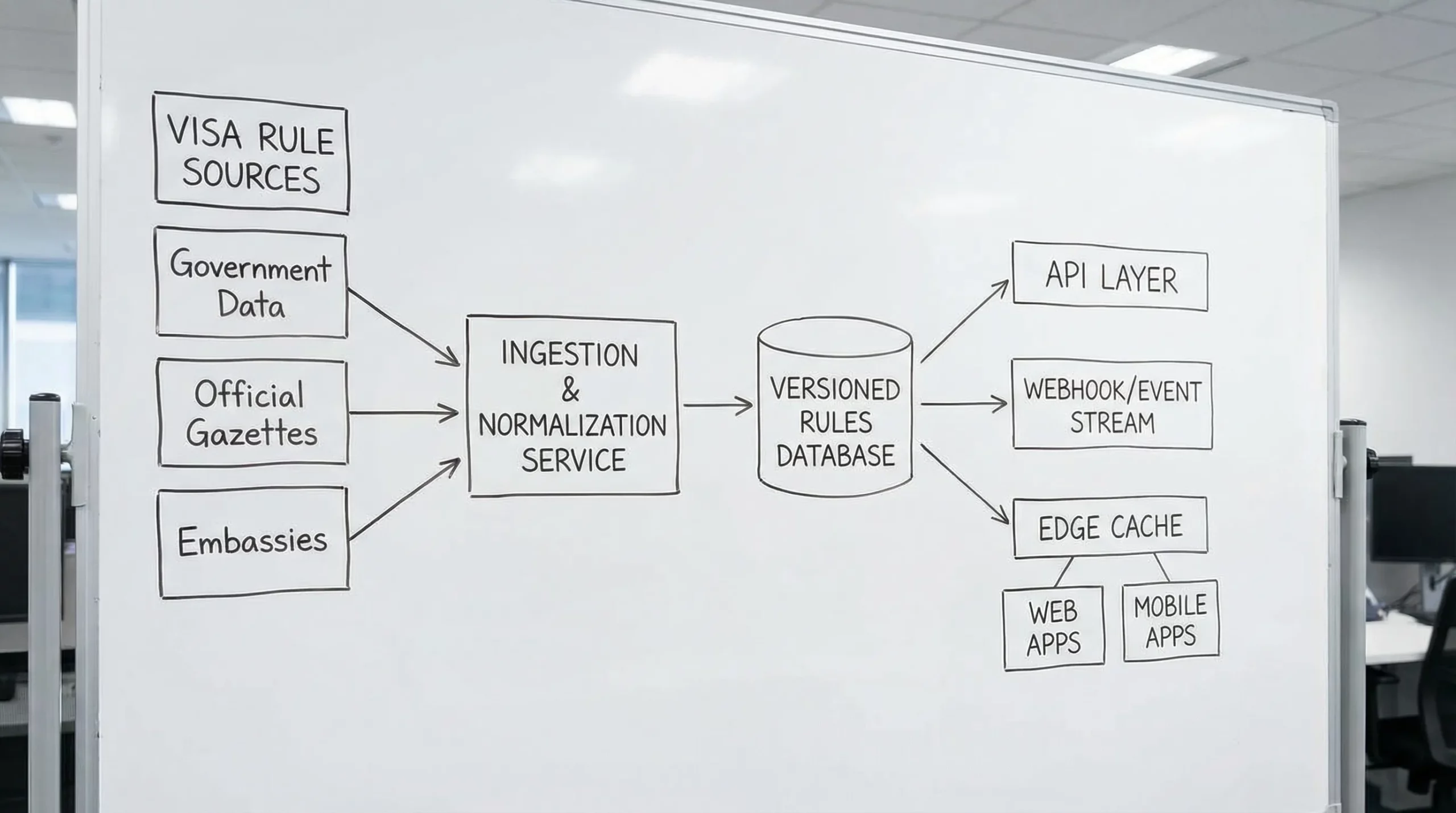
Most successful implementations end up with a layered approach:
- A rule source (government portals, aggregators, specialist providers, internal policy ops)
- An ingestion and normalization layer (turning messy inputs into a canonical schema)
- A publishing layer (versioned rules, backward-compatible contracts)
- A delivery layer (API reads, webhooks/events, and caches)
- An audit and monitoring layer (what changed, when, why, and impact)
Pull, push, or hybrid sync?
Here is how the three sync patterns compare.
| Sync pattern | How it works | Best for | Main risk | Typical mitigation |
|---|---|---|---|---|
| Pull (polling) | Your app periodically requests latest rules | Simple stacks, low change sensitivity routes | Staleness between polls | Short TTL, conditional requests (ETag/If-Modified-Since), scheduled refresh windows |
| Push (webhooks/events) | Provider notifies you when rules change | High volume, high risk markets, operational tooling | Missed events, ordering issues | Signed webhooks, idempotency keys, replay endpoints, dead-letter queues |
| Hybrid | Pull for baseline, push for “hot updates” | Most travel apps at scale | Complexity | Clear ownership: cache policy + event contract + runbooks |
In practice, hybrid is common: polling provides a safe baseline, webhooks reduce time-to-correction.
Model the rules like a product contract, not a paragraph of text
If you want reliable real-time updates, the most important decision is your canonical schema.
A useful rule model usually includes:
- Query context: origin, destination, transit points, travel dates
- Traveler context: nationality, residence, passport type
- Result: required document type, whether an application is needed, and constraints
- Evidence metadata: last updated timestamp, source attribution, rule version
Two design tips that prevent painful replatforming later:
1) Treat “effective date” as first-class
Many rules are announced before they take effect. If you only store the “current” rule, you cannot answer future-dated queries reliably.
Store:
effective_fromeffective_to(nullable)published_at
Your app then answers: “For travel on date X, what rule set applies?”
2) Separate determinism from explanation
You need both:
- Machine-decision fields (document required yes/no, type, constraints)
- Human-readable explanation (help text, links, caveats)
This lets you change copy without changing logic, and it keeps API consumers stable.
Build an update pipeline that assumes rules will be wrong sometimes
Even excellent data providers will occasionally push clarifications or corrections. Your pipeline should handle that without drama.
A mature pipeline has five stages:
Ingest
Normalize different inputs into your canonical schema. Keep raw payloads for traceability.
Validate
Run automated checks:
- Schema validation
- Logical constraints (for example, “visa-free” cannot also require an application ID)
- High-traffic corridor regression checks (your top routes)
Diff
Compute “what changed” at a field level so product, ops, and support can understand impact.
Approve or auto-publish
Not every change needs human approval, but some do. A common pattern is:
- Auto-publish low-risk fields (copy, links, formatting)
- Require approval for eligibility logic changes in top corridors
Publish with versioning
Expose rules via:
- A stable “latest” endpoint
- A versioned endpoint for reproducibility (
/rulesets/{version})
That versioning also becomes your incident rollback lever.
Delivery: keep your app fast without serving stale answers
Visa checks are often called at high-traffic moments (search, checkout, post-booking, check-in). You need a caching approach that respects both performance and correctness.
Use tiered caching
A typical setup:
- Edge cache/CDN for anonymous, low-personalization lookups
- Application cache (Redis or in-memory) for computed results
- Database for source of truth and audit
Cache keys must include the variables that matter
At minimum, key on:
- Nationality
- Destination
- Travel date (or date bucket)
- Transit (if you support multi-leg)
- Purpose (if you differentiate)
If you omit a variable, you will serve incorrect results confidently.
Prefer “stale-while-revalidate” for customer experience
Many apps benefit from returning a cached answer quickly, then revalidating in the background. If the revalidation finds a change, you can:
- Update the cache
- Trigger a user notification if it affects eligibility
This approach is especially useful post-booking.
When to re-check rules across the customer journey
Real-time sync is not only about “latest data,” it is also about checking at the right times.
| Journey moment | Why it matters | Recommended behavior |
|---|---|---|
| Search / inspiration | Early eligibility prevents wasted browsing | Lightweight check, conservative messaging |
| Checkout | Highest conversion sensitivity | Strong freshness guarantees, short TTL |
| Post-booking (T+0 to T+7) | Time to apply for eVisas/eTAs | Trigger application flow, send reminders |
| 72h before departure | Many authorizations have practical buffers | Force refresh, notify if status/rules changed |
| Online check-in | Denied boarding risk peaks | Hard refresh, log rule version used |
If you offer online visa processing as an ancillary, aligning these triggers with conversion touchpoints is also where revenue grows.
Push updates safely: webhooks, idempotency, and replay
If your provider supports webhooks, treat them like a production integration, not a convenience.
Minimum requirements:
- Signature verification on every webhook
- Idempotency so retries do not apply the same change twice
- Ordering strategy (sequence numbers or “published_at” reconciliation)
- Replay endpoint or periodic pull reconciliation
If you are integrating with SimpleVisa, their developer guidance emphasizes secure API usage and webhook verification patterns. See the related post: Developer Q&A: Best Practices for Authenticating Against the SimpleVisa API.
Versioning and backwards compatibility: avoid breaking your own app
Rule schemas evolve. New document types appear. Programs rename themselves. Your API contract must handle that.
Practical techniques:
Semantic versioning for the schema
- Additive fields: safe
- Renames/removals: breaking
If you must break, publish v2 alongside v1 and provide a deprecation window.
Feature flags for “new regimes”
When a new authorization launches, enable it gradually:
- Turn on for internal users
- Turn on for a subset of traffic
- Monitor support tickets and conversion
- Expand
This is especially helpful when effective dates are near and messaging needs refinement.
Auditability: you need to prove what the app told the traveler
When something goes wrong, the question is not “what are the rules now?” It is:
- What rules did we show at booking time?
- What rule version was used at check-in?
- What changed in between?
Store an immutable audit record that links:
- Traveler query context (non-PII where possible)
- Rule version returned
- Timestamp
- Surface (web, iOS, support tool)
This is invaluable for dispute handling, airline support cases, and internal QA.
Observability: detect rule-change impact before support tickets spike
Treat visa rules like any other mission-critical dependency.
Monitor:
- Rule update volume (per destination, per hour)
- Cache hit rate and refresh latency
- Webhook failure rate and replay backlog
- “Eligibility changed after booking” events
- Conversion and drop-off around visa steps
If you already track KPIs post-deployment, connect rule-change telemetry to business outcomes. This pairs well with the measurement framework in 5 KPIs to Track After Deploying a Visa Management Platform.
Data sourcing: where teams get stuck
Many teams start with manual research and quickly discover it does not scale.
Airlines have historically relied on industry data services for entry requirements (for example, IATA’s Timatic is widely used operationally). But product teams often need more than a static reference, they need:
- Machine-readable outputs
- Update diffs
- Clear applicability rules
- Embeddable flows for eVisa/ETA applications
This is where travel document automation providers fit. If you want a grounding on the broader category, see What Is Travel Document Automation? Definitions, Benefits, and Myths.
Build vs buy: the decision hinges on “real-time” ownership
A quick way to decide is to ask who will own these responsibilities:
- Monitoring global policy changes
- Normalizing rules into a stable schema
- Publishing updates with versioning and audit
- Providing integration options (API, hosted, no-code)
If you want to keep visa and border requirements inside your booking flow without turning your team into a policy newsroom, you typically buy.
SimpleVisa’s positioning is specifically in this lane: they provide online visa processing and travel document automation for travel businesses via API integration, a white-label visa application app, and custom data services, with a no-code implementation option for faster time-to-market. You can explore the integration mechanics in How eVisa APIs work: Step by Step.
Implementation checklist (the non-negotiables)
If you implement only a few things from this guide, prioritize these:
- Define a canonical rules schema with effective dates and rule versions.
- Implement hybrid sync (baseline pull plus push updates where possible).
- Build safe delivery: signature verification, idempotency, replay.
- Put cache keys under discipline, include the variables that change outcomes.
- Log rule version at checkout and check-in for auditability.
- Alert on webhook failures and change spikes tied to business metrics.
Closing: real-time visa data is a reliability feature
Travel apps win trust when they prevent surprises. Syncing visa data in real time is one of the highest leverage ways to reduce friction, avoid day-of-travel disruption, and unlock new ancillary revenue opportunities.
If you are evaluating providers, focus less on “coverage claims” and more on engineering realities: update latency, versioning, audit logs, integration patterns, and the operational maturity behind the data.
To see how a specialized provider approaches embedding visa checks and applications in travel flows, start with SimpleVisa’s platform overview at SimpleVisa or review their broader thinking on compliance layers in Travel Tech Stack 2025: Where a Visa Management Platform Fits In.