Visa Data Freshness: SLAs, Caching, and Alerting Explained

Visa and entry requirements are not “content”, they are operational truth. A single stale rule (a newly required eTA, a changed passport-validity rule, a fee update, a new transit exception) can create denied boarding, escalations at the airport, chargebacks, and abandoned bookings.
For travel brands embedding visa guidance into search, checkout, and post-booking flows, visa data freshness becomes a technical discipline. It sits at the intersection of product, engineering, and operations, and it is governed by three levers:
- SLAs/SLOs: what “fresh” and “reliable” means contractually and operationally
- Caching: how you scale requirements lookups without serving outdated answers
- Alerting: how you detect drift before customers do
This guide explains each piece in practical terms, with patterns you can apply whether you consume a travel API, a visa management platform, or a white-label visa app.
1) What “visa data freshness” actually means
In engineering, “freshness” is often simplified to “how recently we updated a record.” For border requirements, that is only half the story.
A useful way to model it is:
- Source update time: when the authoritative rule changed (government portal, carrier bulletin, border agency update)
- Provider ingest latency: how fast your data provider captures and normalizes that change
- Your propagation latency: how fast that update reaches your user experience (API response, widget, email, support scripts)
- Cache staleness: how long an older answer can live at the edge, in your backend, or in the client
Your customer only sees the sum.
Freshness is not one number, it depends on the data type
Visa and entry requirement datasets typically include multiple “classes” of information with different volatility. Treating them all with one caching policy is a common cause of stale answers.
| Data type in a border rules response | Typical volatility | Examples | Suggested freshness posture |
|---|---|---|---|
| Eligibility logic | Medium to high | nationality exceptions, new eTA programs, transit rules | aggressive monitoring, fast propagation targets |
| Document requirements | Medium | photo specs, invitation letter rules, insurance requirement | short to medium TTLs, targeted invalidation |
| Fees and payment methods | Medium | government fee changes, currency/processor updates | shorter TTLs, strong change detection |
| Processing times | Medium | seasonal backlogs, appointment constraints | accept small staleness, show ranges |
| Service availability | High | portal outages, partial suspensions | near real time checks, fast alerting |
| Content and help text | Low | explanatory copy, definitions | longer TTLs OK |
If your flow monetizes applications (ancillary revenue), availability and fee accuracy are especially sensitive. If your flow focuses on eligibility checks, transit rule freshness becomes the priority.
2) SLAs vs SLOs for visa data: what to ask for (and why)
Most teams are familiar with uptime SLAs. Fewer have data SLAs.
- SLO (Service Level Objective) is the internal target a provider aims for.
- SLA (Service Level Agreement) is the contractual commitment, often with remedies.
The Site Reliability Engineering model popularized by Google is a strong reference for turning reliability into measurable objectives (see Google SRE Book).
The 5 SLIs that matter for visa data freshness
Ask your provider to define and report Service Level Indicators (SLIs) that go beyond “API is up.”
| SLI | Definition | Why it matters in travel | Typical measurement approach |
|---|---|---|---|
| API availability | Requests served successfully | Checkout and servicing depend on it | uptime checks, synthetic monitoring |
| Update propagation time | Time from provider ingest to your endpoint | Determines how long stale rules can persist | event timestamps, audit logs |
| Critical change handling | Faster lane for high-impact updates | eTA launches and suspensions cannot wait for batch cycles | incident-style process and reporting |
| Coverage and completeness | Destinations and nationalities supported, plus field completeness | Avoids “unknown” outcomes that force support | coverage dashboards, null-rate metrics |
| Correctness feedback loop | How provider processes disputes/corrections | Border rules are messy, you need a documented escalation path | ticket SLAs, resolution times |
Contract language that prevents “fresh but not delivered” failures
When teams say “our vendor is fresh,” they often mean “vendor updated something internally.” What you need is fresh at your point of use.
Practical SLA clauses to consider (you can tailor the numbers to your risk tolerance):
- Propagation SLA: updates become visible via API/data service within a defined window.
- Critical update SLA: a tighter window for changes that cause denied boarding or legal noncompliance.
- Incident communications: status updates cadence, named channels, and who gets notified.
- Change log access: a machine-readable feed or structured release notes for rule updates.
If you are evaluating a vendor, this fits naturally inside a broader procurement checklist like the one in SimpleVisa’s guidance on choosing a visa processing service.
3) Caching: scaling requirements lookups without serving outdated answers
Caching is unavoidable in travel: peak traffic is spiky, latency matters, and border rules lookups can be called across multiple funnel steps.
The mistake is caching the wrong thing, for too long, with keys that are not specific enough.
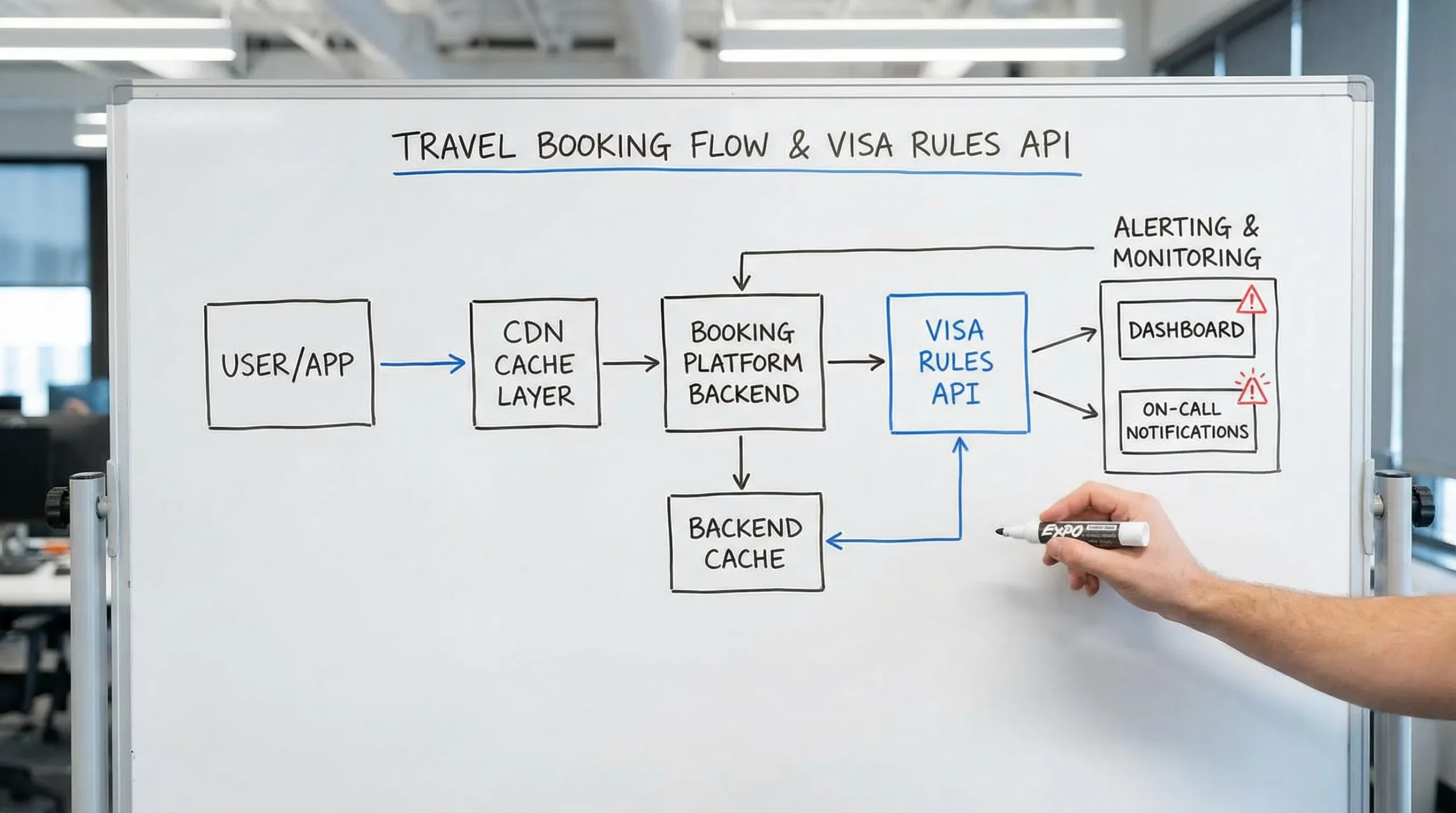
Where visa data gets cached (often unintentionally)
You may have caches in multiple layers:
- Browser or app cache (mobile webviews, service workers)
- CDN/edge cache (if responses are cacheable)
- Your backend cache (Redis, in-memory)
- Provider-side caching (your vendor may do it too)
Unless you design for it, you can end up with “cache stacking” where the effective staleness is far larger than any single TTL.
Cache keys: why “destination only” is dangerous
Visa requirements commonly vary by:
- traveler nationality (passport)
- residency
- destination and transit points
- entry date (policy changes often have effective dates)
- trip purpose and length of stay
If you cache only by destination, you can serve a correct rule for one nationality to a different one. That is worse than returning “unknown.”
A safer pattern is to cache only on inputs that fully determine the answer. If your flow supports many attributes, consider caching at the provider abstraction layer rather than within UI components.
TTL strategy: use different policies for different volatility
Instead of one global TTL, use policy tiers:
| Tier | What you cache | Typical use case | Risk | Mitigation |
|---|---|---|---|---|
| Long TTL | static help content, definitions | education pages, tooltips | low | periodic refresh |
| Medium TTL | stable rule components | low-change destinations | medium | background revalidation |
| Short TTL | fees, availability, eligibility | high-impact steps in checkout | high | forced refresh, alerting |
If your platform uses HTTP caching, patterns like Cache-Control: max-age with stale-while-revalidate can reduce latency while still rechecking in the background (see RFC 9111 HTTP Caching).
Prefer “stale while revalidate” over “stale until it hurts”
A practical pattern for visa checks in booking flows:
- Serve cached data when it is within TTL.
- If TTL expired, serve last known good only if it is still within an absolute staleness limit, and trigger a refresh.
- If the absolute limit is exceeded (or the provider indicates a critical update), force a live call or show a “check again” state.
This is a better customer experience than hard failures, but it prevents stale data from surviving for days.
4) Alerting: detect freshness regressions before customers do
Alerting for visa data should not only page you when the API is down. It should tell you when the data is getting older than your product promise.
Google’s SRE guidance is clear that alerting should be actionable and tied to user impact, not to every metric deviation (see Monitoring Distributed Systems). The same applies here.
Three alert classes you want
1) Freshness budget alerts (data staleness)
Track a metric like:
data_age_seconds(now minus “last updated” timestamp per market or rule bundle)
Alert when it exceeds your threshold by tier (short vs medium volatility), and especially when it exceeds an “absolute max age.”
2) Propagation alerts (provider to you)
Even if the provider is updating quickly, you can still lag if:
- your caches are too sticky
- your jobs that pull data fail silently
- your booking frontend deploy froze a config
Alert on:
- “no successful refresh in N minutes”
- “refresh failures > X%”
- “ETag/Last-Modified has changed but cache did not invalidate”
3) Customer-impact alerts (leading indicators)
Some freshness failures show up as behavior changes before you can confirm the rule changed:
- spikes in “am I eligible” support tickets
- sudden increases in form abandonment for a destination
- higher “manual review” rates (if you run visa applications)
If you already track KPIs after deployment, you can wire these to early warning alerts. SimpleVisa’s KPI guide provides a useful framing for this layer of monitoring, even if you implement it in your own BI stack: 5 KPIs to Track After Deploying a Visa Management Platform.
Don’t forget vendor status and industry sources
Many travel brands also maintain a “sanity check” against reputable industry sources. In airline operations, for example, IATA’s Timatic is widely used as a reference dataset (see IATA Timatic). You do not need to duplicate it, but you can use it as an escalation input when disputes arise.
5) A practical incident playbook for stale visa data
When an alert fires, you need a playbook that prioritizes customer safety and revenue protection.
Step 1: Identify the blast radius
- which destinations and nationalities are affected
- which funnel steps use the data (search, checkout, post-booking, servicing)
- whether the issue is “wrong answer” vs “missing answer”
Step 2: Choose a containment action
Common containment actions include:
- Force refresh (invalidate caches for the affected keys)
- Quarantine a market (temporarily disable automated guidance for a destination and route to assisted flow)
- Fallback logic (switch to a backup data source, or require a live recheck)
- UX downgrade (display a “we are rechecking rules” state instead of presenting potentially stale requirements)
Step 3: Communicate in the right places
- customer-facing: transparent, minimal, focused on what to do next
- internal: support macros, escalation rules, and ETA for fix
- partner-facing (if you syndicate): a clear incident note and resolution timeline
If you support travel businesses via embedded flows, this is where integration choice matters. API consumers can invalidate and redeploy quickly. White-label users may need the provider to roll out a rules update centrally.
6) Implementation blueprint by integration model
Your caching and alerting design should match how you deliver visa functionality.
If you use an API in the booking flow
- Cache only at the backend, not in UI, unless you have strict versioning.
- Implement ETag or equivalent conditional fetches where available.
- Emit events for every rules lookup (inputs, timestamps, response version), so you can audit.
If you are building around an API provider, it also helps to align auth, token rotation, and request signing with the vendor’s operational expectations. For SimpleVisa-specific API hygiene, their developer guidance on authentication illustrates the kind of operational detail that reduces incidents: Best Practices for Authenticating Against the SimpleVisa API.
If you use a white-label visa application app
- Prefer provider-managed freshness and central change deployment.
- Ask for visibility: change logs, dashboards, and incident communications.
- Focus your engineering on alerting from the outside (synthetic checks) and on customer messaging.
If you use a no-code widget
- Treat the widget as a “freshness boundary.” Do not cache its outputs in the browser.
- Monitor embed health (load time, error rates) separately from rules freshness.
- Track conversion and abandonment as early indicators.
SimpleVisa supports multiple models (API integration, white-label visa application app, and a no-code implementation option), so teams often pilot quickly and then mature into deeper integrations as volume grows. If you are deciding between models, this comparison can help frame trade-offs: API vs. White-Label App: Which Visa Integration Model Suits You?.
7) The “minimum viable freshness stack” for travel brands
If you want a pragmatic starting point, build this in layers:
- Define freshness tiers per data class (eligibility, fees, availability, content).
- Set SLOs (internal targets) for maximum data age and propagation time.
- Implement cache tiering with explicit keys and absolute max staleness.
- Add three alerts: staleness budget breach, refresh job failure, customer-impact anomaly.
- Write a 1-page playbook with containment actions and escalation contacts.
This is enough to prevent most “we served last month’s rule” incidents, and it creates the measurement foundation you need to negotiate stronger SLAs with providers.
Where SimpleVisa fits
If you are operationalizing visa data freshness across your booking and servicing journeys, SimpleVisa’s positioning is aligned with the problem: travel document automation and visa processing delivered via API integration, white-label app, and custom data services.
To see how a visa management approach typically plugs into the broader compliance layer of a modern travel stack, start here: What Is Travel Document Automation? Definitions, Benefits, and Myths. From there, you can evaluate the right integration model and the SLA and monitoring requirements that match your risk profile.